USENIX Security '22 - Open to a fault: On the passive compromise of TLS keys via transient errors |
|
|
USENIX Security '22 - Open to a fault: On the passive compromise of TLS keys via transient errors
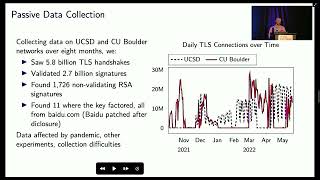
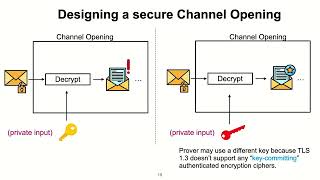
George Arnold Sullivan, University of California, San Diego; Jackson Sippe, University of Colorado Boulder; Nadia Heninger, University of California, San Diego; Eric Wustrow, University of Colorado Boulder It is well known in the cryptographic literature that the most common digital signature schemes used in practice can fail catastrophically in the presence of faults during computation. We use passive and active network measurements to analyze organically-occuring faults in billions of digital signatures generated by tens of millions of hosts.We find that a persistent rate of apparent hardware faults in unprotected implementations has resulted in compromised certificate RSA private keys for years. The faulty signatures we observed allowed us to compute private RSA keys associated with a top-10 Alexa site, several browser-trusted wildcard certificates for organizations that used a popular VPN product, and a small sporadic population of other web sites and network devices. These measurements illustrate the fragility of RSA PKCS#1v1.5 signature padding and provide insight on the risks faced by unprotected implementations on hardware at Internet scale. View the full USENIX Security '22 program at https://www.usenix.org/conference/usenixsecurity22/technical-sessions |